Procedure for Managing a Privacy Breach – March 26, 2026
Page 1 of 7
PROCEDURE
FOR
MANAGING
A
PRIVACY
BREACH
Procedure
Type:
Management
Initially
Approved:
June 11,
2021
Procedure
Sponsor:
General Counsel
and University
Secretary
Last Revised:
March 26,
2026
Primary
Contact:
The Access and
Privacy Office
Review
Scheduled:
March 26,
2031
Approver:
Executive Leadership Team
A.
PROCEDURES
1.
REPORTING A PRIVACY BREACH
1.1
A privacy breach occurs when there is unauthorized access to or collection, use,
disclosure or destruction of Personal Information in contravention of the Act.
1.2
All notifications concerning privacy breaches must be sent either to the Access and
Privacy Office by email at (privacy@mtroyal,ca) or through the online Privacy Breach
Report process.
1.3
If an Employee believes that there has been a privacy breach, they must make
reasonable efforts to immediately contain the identified breach and then submit a
Privacy Breach Report to the Access and Privacy Office. Employees must also notify
their supervisor.
1.4
If an individual believes that there has been a breach of their own Personal
Information by the University, they may submit a Privacy Breach Report to the
University’s Access and Privacy Office.
1.5
An individual may seek advice from the Access and Privacy Office in advance of
submitting a Privacy Breach Report or where immediate steps are needed to address
an ongoing breach. The Access and Privacy Office can be contacted at
privacy@mtroyal.ca
.
2.
RECEIPT OF A PRIVACY BREACH REPORT
2.1
Upon receipt of a Privacy Breach Report, the IMPA will review the alleged privacy
breach to determine if a breach occurred and, if so, what further action is required to
mitigate future breaches.
2.2
If the IMPA has a conflict of interest, a Senior Leader of the Access and Privacy
Office will act with the same authorities prescribed to the IMPA for the purposes of
this Policy and Procedures.
2.3
When a privacy breach has been substantiated, the IMPA will:

Procedure for Managing a Privacy Breach – March 26, 2026
Page 2 of 7
a. work with the impacted Department(s) to identify any further steps needed to
address the breach;
b. ensure that the University provides any applicable notification as required under
the Act to appropriate parties;
c. assess the processes currently established in regards to safeguarding the
Personal Information subjected to the privacy breach, in consultation with the
impacted Department(s); and
d. Where the IMPA determines that disciplinary action may be appropriate, they will
notify the relevant manager or other appropriate department such as Human
Resources or the Office of Student Community Standards for investigation of the
matter under the appropriate University policies.
2.4
If the IMPA determines that the alleged breach to be unsubstantiated, they will notify
the person who submitted the Privacy Breach Report in writing that no privacy breach
has occurred, and no further action will be taken.
2.5
Where a privacy breach report is determined to have been submitted in bad faith,
the IMPA may consult with the necessary leaders on campus to enact proceedings
under any other applicable University Policy, including Code of Conduct –
Employees and Code of Student Community Standards Policy.
3.
CONTAINING A PRIVACY BREACH
3.1
The IMPA will notify, as applicable, any impacted Department(s), relevant subject
matter experts, or third parties of a confirmed privacy breach.
3.2
The IMPA, impacted Department(s), and subject matter experts are expected to
consult and coordinate the institutional response to a privacy breach.
3.3
The impacted Department(s) will take reasonable steps to contain the breach in a
timely manner.
3.4
Steps to contain the privacy breach may include, but are not limited to, the following:
a. recovering, retrieving or destroying any Records or otherwise taking steps to
contain the privacy breach;
b.
requesting an unauthorized recipient of a Record containing Personal
Information to delete the Record and confirm the deletion in writing;
c. limiting access to software systems (e.g. change passwords, access,
identification numbers, or shut down system);
d. revoking access;
e.
temporarily shutting down a website or system;
f. assessing security protocols concerning the breach and implement interim
solutions for any immediate process weaknesses (physical, technical,
administrative); and/or,
g. temporarily shutting down a website or system

Procedure for Managing a Privacy Breach – March 26, 2026
Page 3 of 7
3.5
If the privacy breach involves digital Records or systems, Employees must contact
Information Technology Services for support to contain the privacy breach in a timely
manner.
4.
NOTIFICATION OF THE PRIVACY BREACH
4.1
The IMPA is responsible for determining whether and how notices of a privacy
breach will be sent.
4.2
The IMPA will provide notices where a privacy breach has occurred and there is a
Real Risk of Significant Harm arising from the privacy breach and as otherwise
required under the Act.
4.3
To determine if there is a Real Risk of Significant Harm involves weighing the
following factors:
4.3.1 The likelihood that the breached Personal Information has been or will be
misused;
4.3.2 Whether the privacy breach was caused as a result of malicious intent;
4.3.3 The effectiveness of containment established or mitigation measures
enabled in response to the privacy breach;
4.3.4 The sensitivity of the personal information at issue concerning the privacy
breach that includes, but is not limited to, biometric, financial, health
information or other personal information in regards to a vulnerable
individual;
4.3.5 The number of individuals impacted by the privacy breach; and
4.3.6 Whether the incident involves a system-wide issue that has resulted in the
unauthorized disclosure or exposure of Personal Information at a broad or
public environment level.
4.4
In the event of a substantiated privacy breach where there exists a Real Significant
Harm under 4.3, the IMPA will issue notification to the impacted individual(s), the
Commissioner and the Minister. The notification will include the specific contents
prescribed under the Act.
4.5
The IMPA will consult with the Department(s) involved in determining how to
communicate such notifications.
4.6
Notification of individuals impacted by a privacy breach will occur as soon as is
reasonable following the privacy breach. However, if law enforcement authorities
are involved, the IMPA will consult with those authorities to determine whether
notification should be delayed in order not to impede a criminal investigation.
5.
PRIVACY BREACH REVIEW
5.1
Once the immediate steps to contain a privacy breach and any required notifications
have been completed, the IMPA will review and assess the privacy breach to
determine:

Procedure for Managing a Privacy Breach – March 26, 2026
Page 4 of 7
a. the circumstances giving rise to the privacy breach.
b. the number of individuals impacted, the sensitivity of the Personal Information,
and the potential for harm.
c. the safeguards in place prior to the privacy breach.
d. the effectiveness of the steps taken to contain the privacy breach.
e. any immediate, ongoing, and foreseeable risks concerned with Personal
Information in the Department(s).
f. recommendations to prevent a future privacy breach (e.g. privacy training,
security process, technical improvements, policy or process review).
5.2
The above recommendations will be presented to the Senior Leader(s) responsible
for the respective Department(s) concerning the breach.
5.3
The IMPA and the Senior Leader(s) of the Department(s) will work together to ensure
that the necessary changes are implemented to mitigate against a similar privacy
breach occurring in the future.
6.
REPORTING A PRIVACY BREACH TO THE COMMISSIONER
6.1
Individuals who believe that the University has accessed, collected, used or
disclosed their own Personal Information in contravention of the Act may ask the
Commissioner in writing to review the matter.
6.2
Prior to asking the Commissioner to review the alleged privacy breach, the individual
must submit their complaint first in writing to the Access and Privacy Office to provide
an opportunity for the University to remedy the complaint.
6.3
The Access and Privacy Office will respond to the Commissioner directly in regards
to an individual’s request for review submission to the Commissioner’s Office
pertaining to their privacy breach complaint in accordance with the Act.
Procedure for Managing a Privacy Breach – March 26, 2026
Page 5 of 7
B.
DEFINITIONS

Procedure for Managing a Privacy Breach – March 26, 2026
Page 6 of 7
(1)
Access and Privacy
Office:
means the Information Management & Privacy Advisor
and/or Senior Leaders of the Access & Privacy Office
as delegated by the President in writing.
(2)
Act, the:
means the Protection of Privacy Act of Alberta. Also
known as the “POPA” or the Act.
(3)
Commissioner:
means the Information and Privacy Commissioner of
Alberta appointed in accordance with the Act.
(4)
Employee:
means individuals who are engaged to work for the
University under an employment contract, including but
not limited to faculty, staff, exempt, casual and
management employees.
(5)
IMPA
means the Information Management and Privacy
Advisor or designate.
(6)
Personal Information:
means recorded information about an identifiable
individual, including:
a. the individual’s name, home or business
address or home or business telephone
number,
b. the individual’s race, national or ethnic origin,
colour or religious or political beliefs or
associations,
c. the individual’s age, marital status or family
status,
d.
the individual’s gender identity, sex or sexual
orientation,
e. an identifying number, symbol or other
particular assigned to the individual,
f. the individual’s fingerprints, other biometric
information, blood type, genetic information or
inheritable characteristics,
g. information about the individual’s health and
health care history, including information about
a physical or mental health,
h. information about the individual’s educational,
financial, employment or criminal history,
including criminal records where a pardon has
been given,
i. anyone else’s opinions about the individual, and
j. the individual’s personal views or opinions,
except if they are about someone else.
Procedure for Managing a Privacy Breach – March 26, 2026
Page 7 of 7
(7)
Policy:
means the Privacy Policy.
(8)
Record:
means any electronic record or other record in any form
in which information is contained or stored, including
information in any written, graphic, electronic, digital,
photographic, audio or other medium, but does not
include any software or other mechanism used to store
or produce the record.
(9)
Department:
means a faculty within the Academic Division or a
department outside of the Academic Division.
(10)
Senior Leader:
includes ELT and any other leader who either (i)reports
to a Vice-President or the President and leads a
department and (ii) any other person designated as a
Senior Leader by ELT.
(11)
University:
means Mount Royal University.
C.
RELATED POLICIES
● Access to Information policy
● Information Security policy
● Privacy policy
D.
RELATED LEGISLATION
● Protection of Privacy Act, SA, 2024, c F-25
●
Access to Information Act, SA, 2024, c A-1.4
E.
RELATED DOCUMENTS
F.
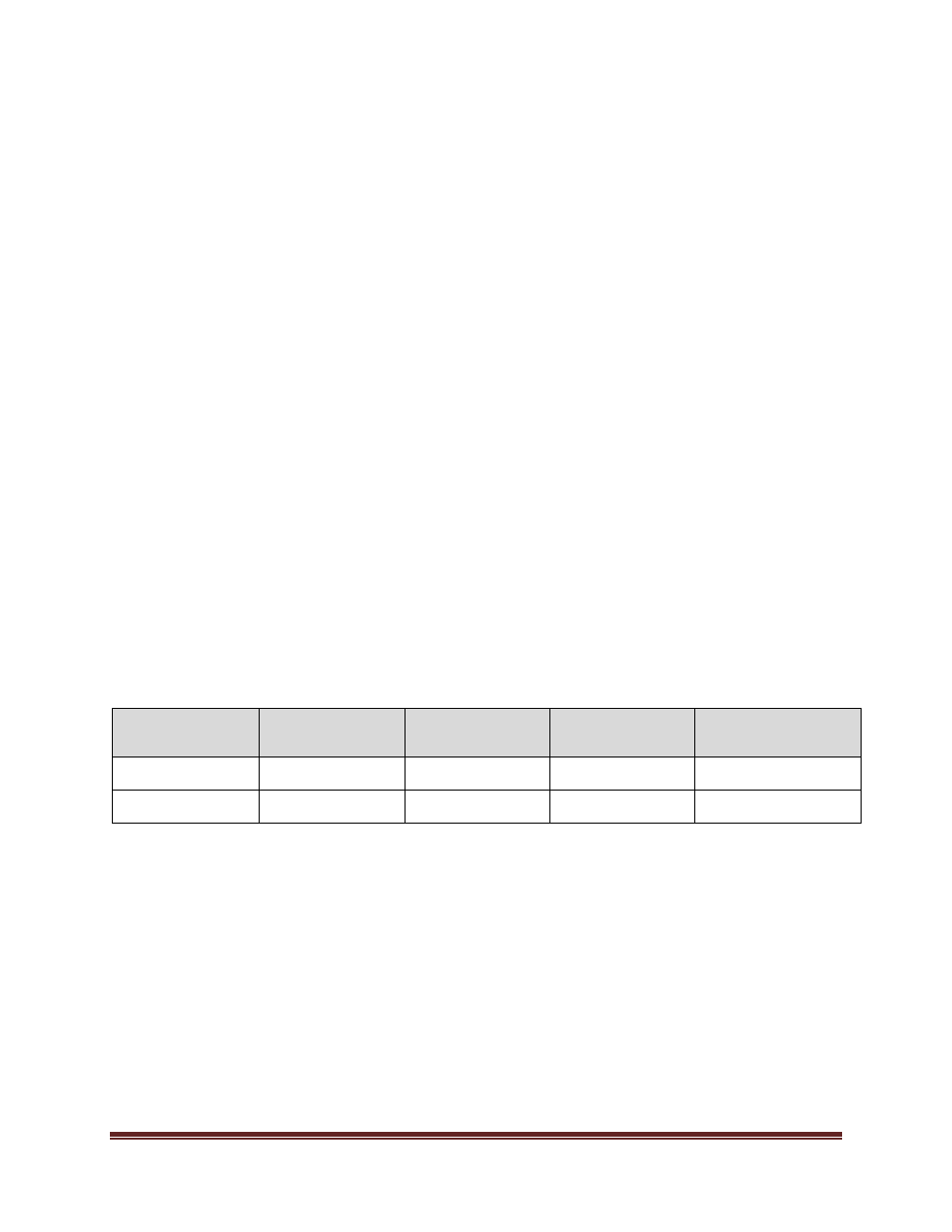
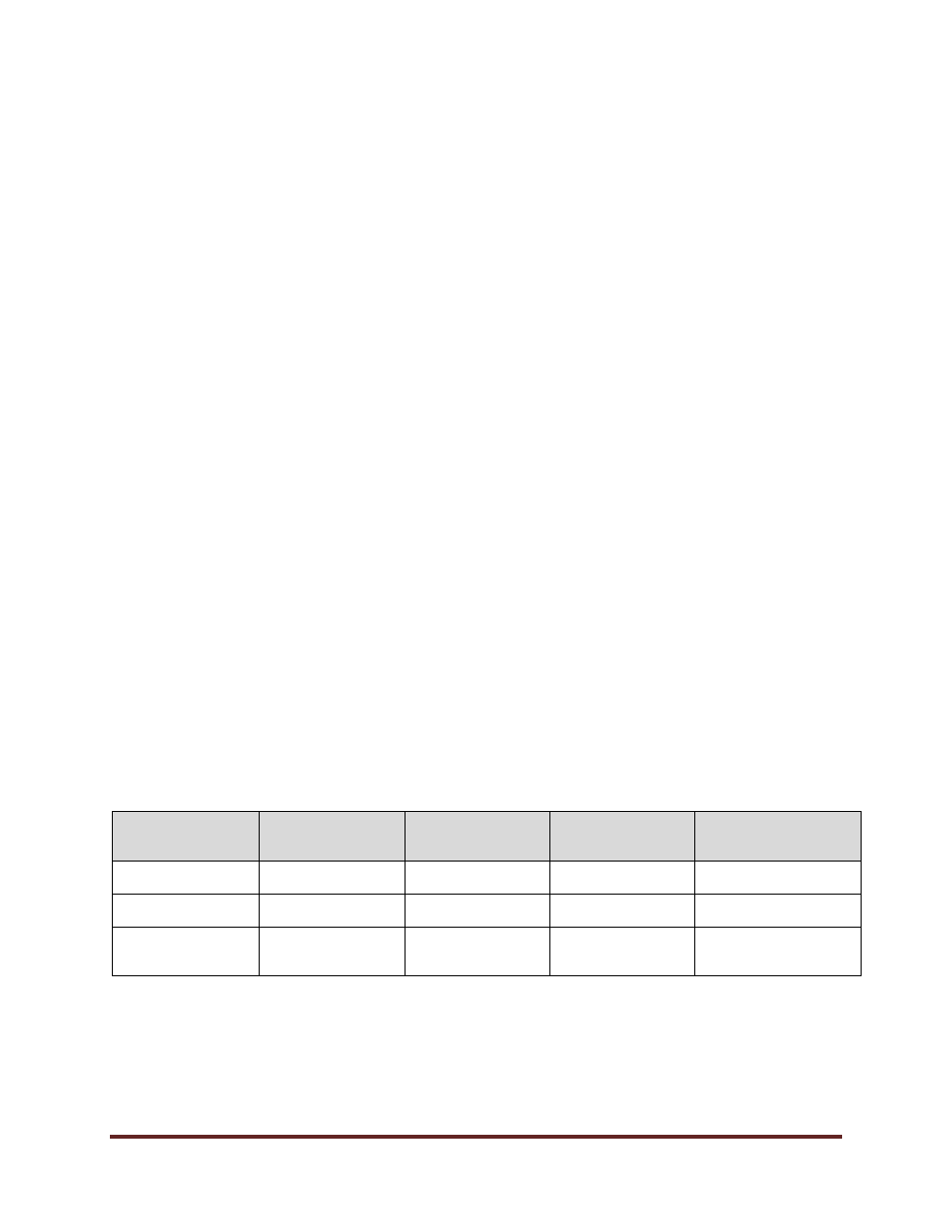
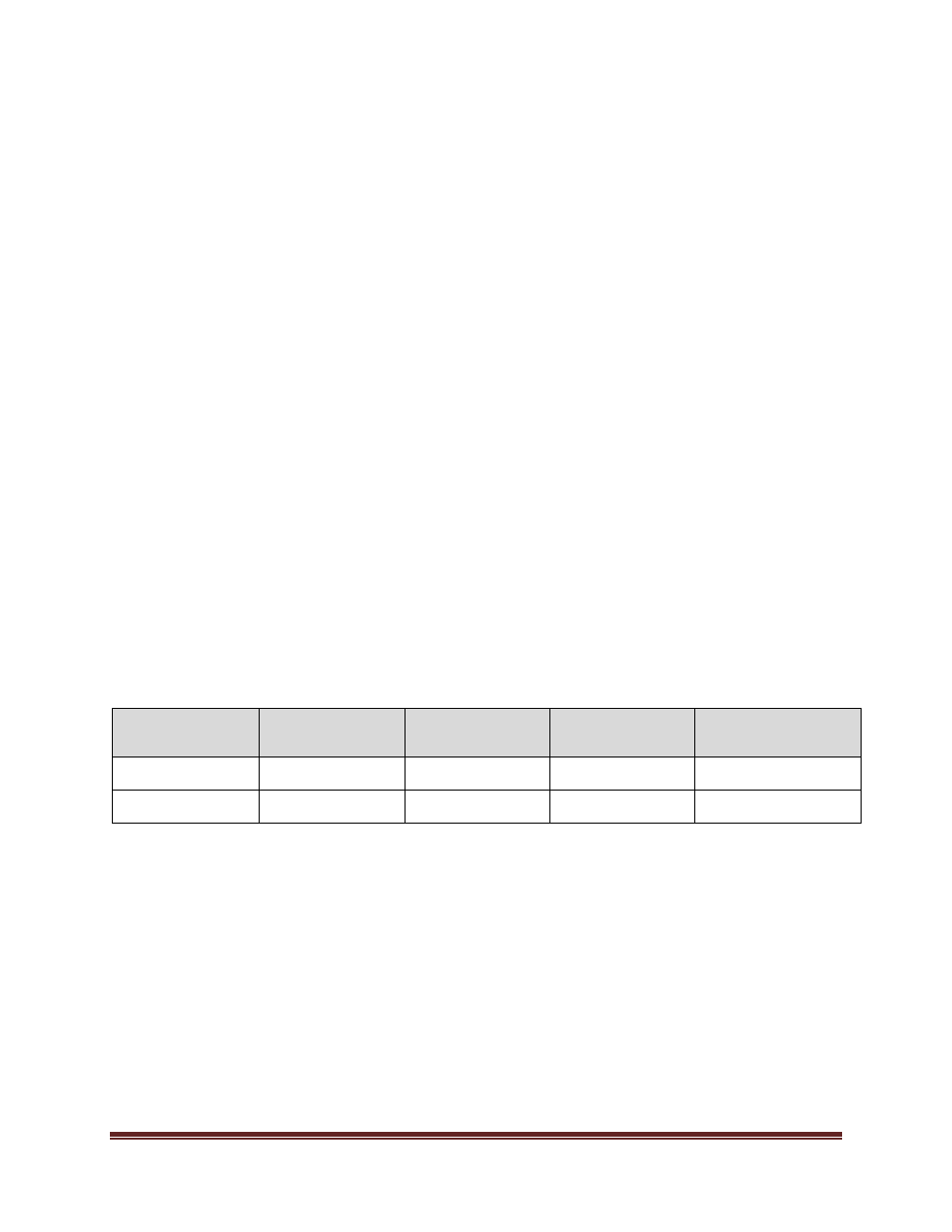
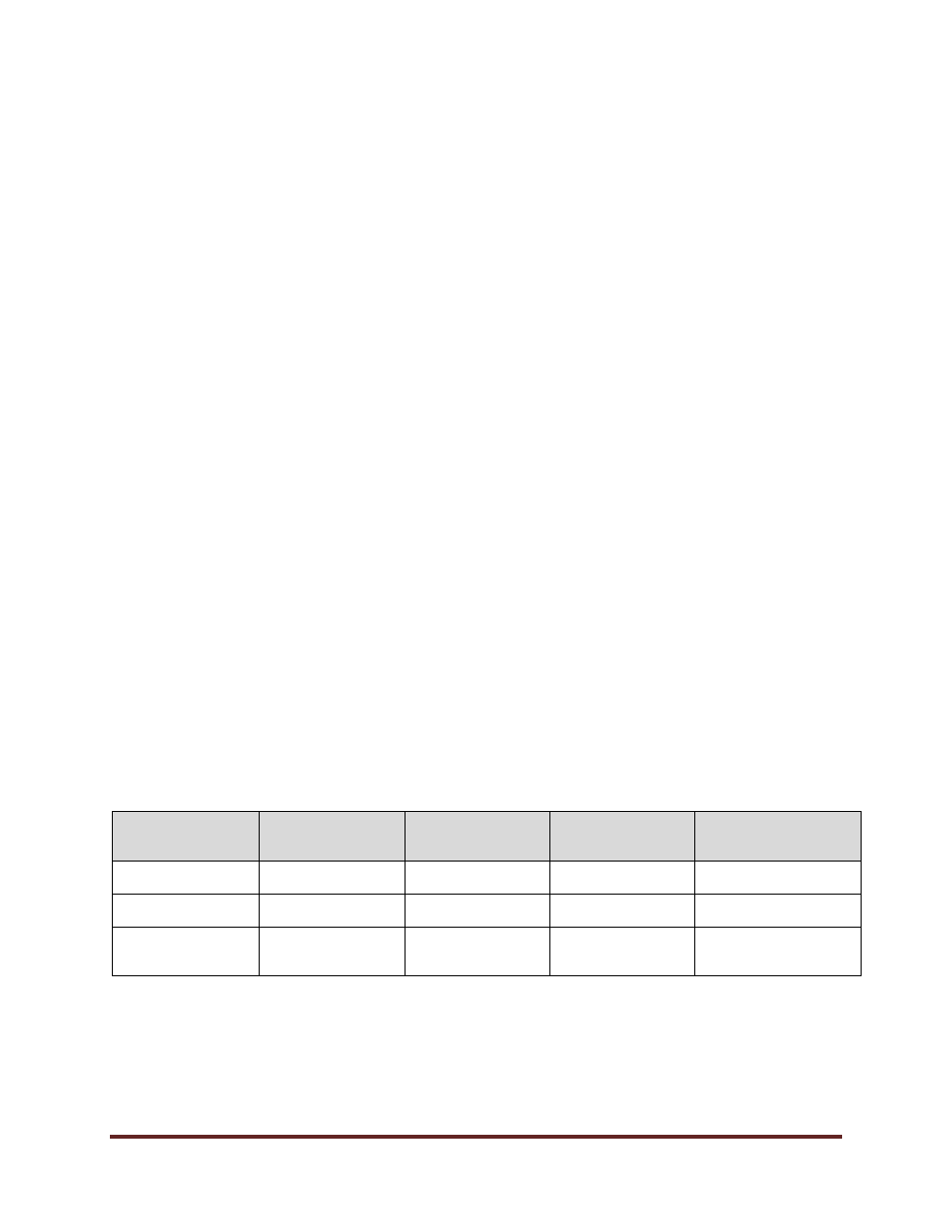
REVISION HISTORY
Date
(mm/dd/yyyy)
Description of
Change
Sections
Person who
Entered Revision
(Position Title)
Person who
Authorized Revision
(Position Title)
01/19/2022
Editorial
Related Policies
Policy Advisor
General Counsel and
University Secretary
04/20/2023
Editorial
Definitions
Policy Advisor
General Counsel and
University Secretary
03/26/2026
Major
All
Information
Management &
Privacy Advisor
Executive Leadership
Team